Effective Governance, Risk & Compliance (GRC)
Addressing governance, enterprise risk management, and effective corporate compliance can be painful. Instead of point solutions, think about integrating your data onto a single platform that lets you “see” across your silos. Painless, effective and the solution to address all facets of Regulatory Reporting and Governance, Risk, and Compliance (GRC).

The Most Secure NoSQL Database
World-class enterprises and government agencies around the world trust MarkLogic to integrate their mission-critical data with industry-leading, unparalleled security as verified by Common Criteria Certification.
- Advanced encryption
- Fine-grained, role-based security
- Data anonymization and redaction

What is GRC and why does it matter?
Governance
Governance is stuff you do to mitigate Risk and manage Compliance. Governance is proportional to an organization’s total Risk + Compliance.
Risk
Risk is bad stuff you don’t want to happen. This is driven by market dynamics and the “unexpected.” Higher risk is usually a result of less compliance.
Compliance
Compliance is just stuff you have to do because someone says so. This is driven by regulatory and legislative bodies. Higher compliance results in less risk.
Success Story
Intel & MarkLogic
MarkLogic and Intel assist financial institutions in establishing a sound application framework that makes it possible to respond to regulators in an efficient, timely, and responsive manner. A solid, complete solution architecture for Regulatory Reporting.
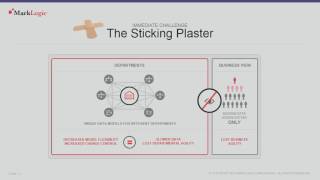
Data Governance in an Unpredictable World
Watch as Solutions Director, Damon Feldman, PhD, demonstrates how to use MarkLogic to implement, enforce and verify policies around data security, sharing, provenance and retention.
Compliance-Ready for Highly Regulated Markets and the Government
Our customers have received Authority to Operate (ATO) for information systems utilizing MarkLogic that involve almost all of the major systems security standards, including:
SOC 2 Type II
The MarkLogic SOC 2 Type II report is an independent assessment of our control environment performed by a third party. It is based on the AICPA’s Trust Services Criteria and addresses the key trust principles of security, availability, confidentiality, processing integrity, and privacy.
FDA Title 21 CFR Part 11
Attestation for compliance with US Food and Drug Administration regulations around handling electronic records.
NIST 800-53
The NIST Cybersecurity Framework (CSF) is US-issued guidance for organizations on how to improve their ability to prevent, detect, and respond to cybersecurity risks. NIST 800-53 maps to other standards (e.g., ISO 27001) and underlies other standards like HIPAA and FedRAMP.
FedRAMP
Security framework established by the General Services Administration (GSA) in 2012 to protect data confidentiality, integrity, and availability in cloud environments.
HIPAA
Guidelines for complying with the US Health Insurance Portability and Accountability Act of 1996 (HIPAA) related to processing, maintaining, storing, and sharing protected health information (PHI).
MarkLogic is HIPAA-ready.
DFARS
The Defense Federal Acquisition Regulation Supplement is US DoD-specific rules for procurement within the US public sector.
Self-attestation with DFARSCommon Criteria
International standard (ISO/IEC 15408) for a common set of functional and assurance security requirements, evaluated by licensed labs.
MarkLogic is the only non-relational database to have this.
STIG
Documented guidelines for deploying in U.S. DoD/DISA IT systems that provide guidance on how to set up and configure a product.
MarkLogic has been “STIG’d” for multiple US federal projects.
Section 508
A Voluntary Product Accessibility Template (VPAT®) explains how information and communication technology products meet the accessibility requirements of the U.S. government Section 508 standards.
Download VPATGDPR
General Data Protection Regulation (GDPR) that went into effect in May 2018 with the goal of strengthening personal data protection in Europe.
MarkLogic complies with GDPR, and helps customers comply with GDPR.

Data Agility with MarkLogic
Don’t waste time stitching together components. MarkLogic combines the power of a multi-model database, search, and semantic AI technology in a single platform with mastering, metadata management, government-grade security, and more.