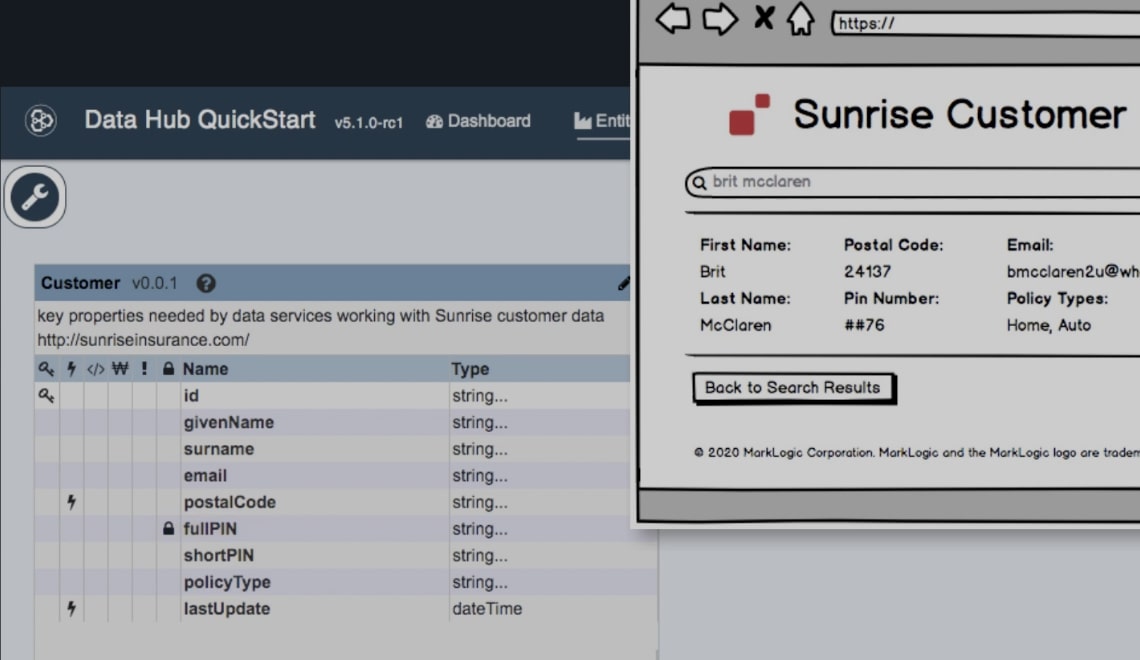
MarkLogic Data Hub Software
Data Hub Software is the UI for the Data Hub Platform. It’s a visual interface to build data pipelines for ingestion, harmonization, and mastering. It’s data integration and management made easier.

What is MarkLogic Data Hub Software?
Data Hub Software gives you the power to map incoming data to future-state, domain-driven data models, defined in the language of the business. You can track data lineage, maintain best-in-class data security, and explore harmonized data. Best of all: you can do it without writing code.
The Latest in Agile Data Integration
The old way to approach integration was to model all of your data upfront, then run your ETL processes, and then eventually build your API and hope for the best. MarkLogic takes a faster, more agile approach that delivers immediate business value. You start by defining your business goal and the data services you need, then you model and curate just the requisite source data those services require. This data services-first (a.k.a. API-first) approach applies agile development principles to data integration and data management.
Fast Data Pipelines
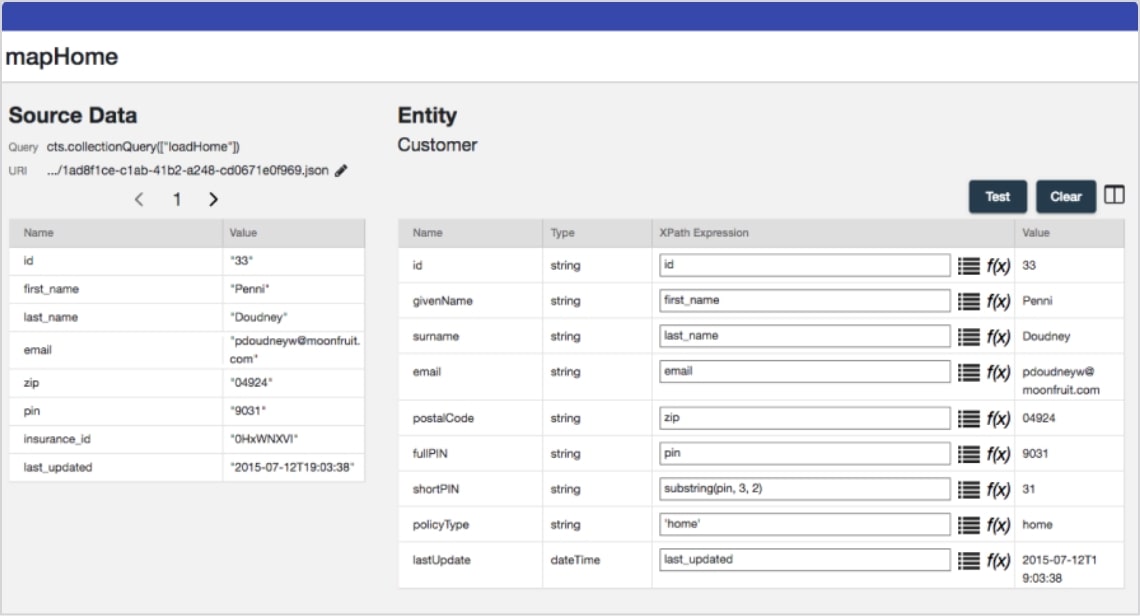
Ingest raw data quickly. Run harmonization flows to turn your raw data into harmonized data. Utilize model-driven mapping to define mapping expressions. Use an agile process to continue refining your harmonized entities over time.
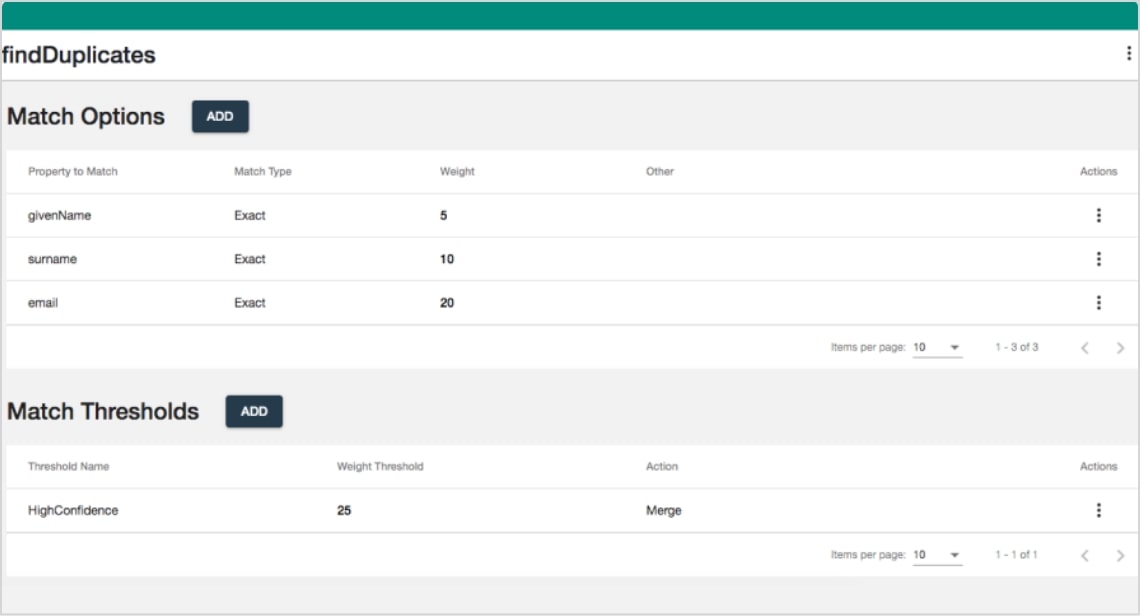
Built with Smart Mastering
No need to use a separate master data management tool. Do your matching and merging right in the Data Hub, leveraging smart probabilistic matching algorithms and the ability to un-merge data when needed (no raw data is ever thrown out).
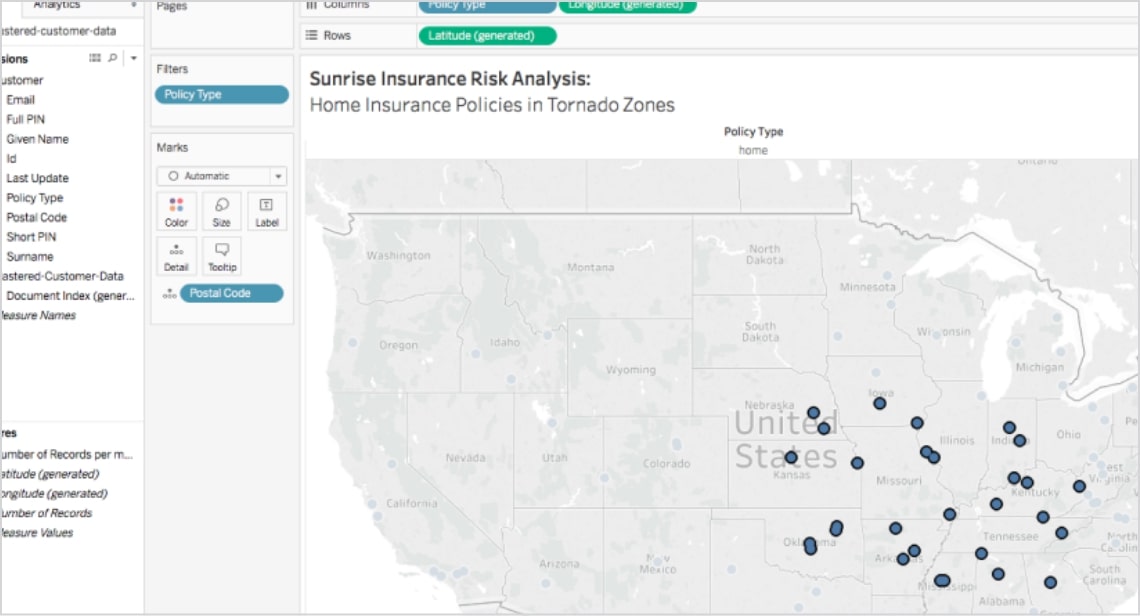
Data Services Delivered
After ingesting, mapping, and mastering, you now have harmonized data based on a common enterprise entity model. Now, it’s time to build data services on those durable data assets. MarkLogic supports a wide variety of programming languages and APIs, including JavaScript, Node.js, and Java.

“We developed a MarkLogic Data Hub for faster application development and delivery. The first implementation from scratch to live took nine months (versus years), and the next took four months with a completely new development team.”
Senior application software delivery advisor


Data Agility with MarkLogic
Don’t waste time stitching together components. MarkLogic combines the power of a multi-model database, search, and semantic AI technology in a single platform with mastering, metadata management, government-grade security, and more.